Reading through this link Raphael Mudge talks about using rogue applications called notepad.exe to call back out, and then drops this tidbit(emphasis mine):
netstat -nab is a tool to help you discover rogue notepad.exe instances connecting to the internet
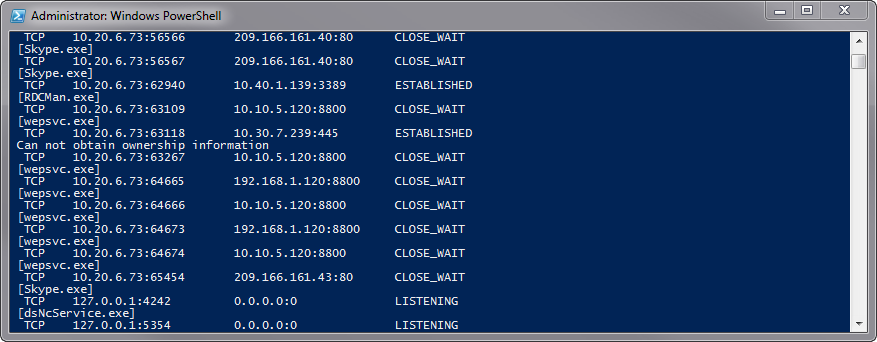
the output of which looks something like this:
I think to myself, this is a fantastic tool to use for troubleshooting, however, the default output is huge. I need to pare it down a bit. In Bash, I would just pipe to grep and be done. I’m very new at PowerShell, but it seems overly optimistic to thing it has grep.
After a bit of searching, no, there’s no grep. However, somewhere in the StackExchange network there was a more appropriate solution. “Out-String” and “Select-String”. Mixing all that together gave me the following:
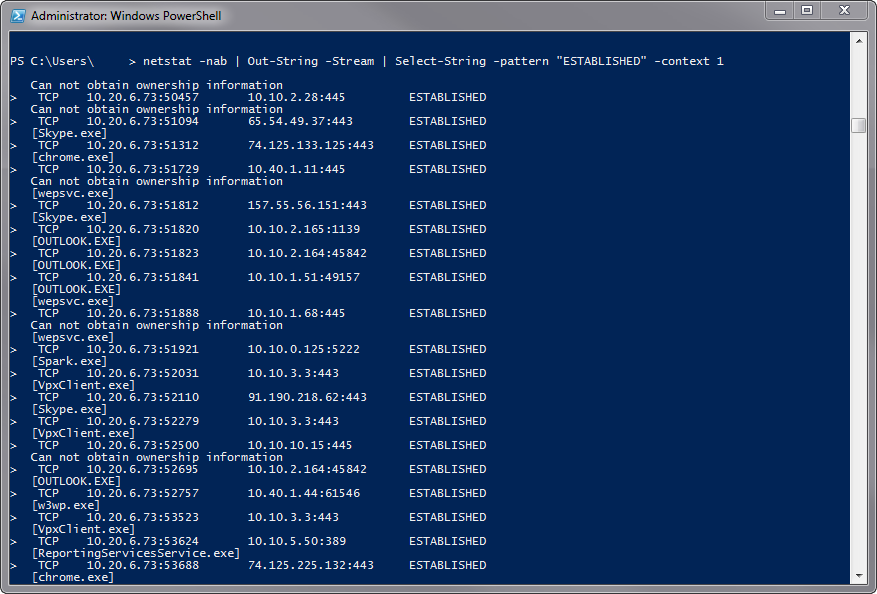
netstat -nab | Out-String -Stream | Select-String -pattern “ESTABLISHED” -context 1
So what does all that mean, exactly?
netstat: “Displays protocol statistics and current TCP/IP network connections
-
-n : shows addresses and ports as numerical infomation
-a : all connections and ports
-b : show executable involved
Out-String: Sends objects as strings (pipes the output of netstat as strings instead of data)
- -stream : sends each string individually rather than concatenating to a single string
Select-String: …You can use it like Grep in UNIX…
- -Pattern “” : inside the quotes goes what you’re looking to filter with
-context # : this is the number of lines after your match that you want to return.
So, as a baby step into PowerShell and learning how it is not Bash, this was fun. More of these to come as I get better at it.
